During the process of analyzing a network problem with a network analyzer tool or a protocol sniffer, especially when we find a suspicious worm or backdoor activity, we get only useful information like MAC addresses, IP addresses and also the port number in transport layer. The analyzer may not even know which application layer protocol is used, even it tells, we still need to figure out which application or process is using this application layer protocol. Is there any method that we can find out the original application or process using that TCP or UDP port? If you are conducting an on-site analysis, Capsa can easily help find out which process is using what port.
Let’s see how.
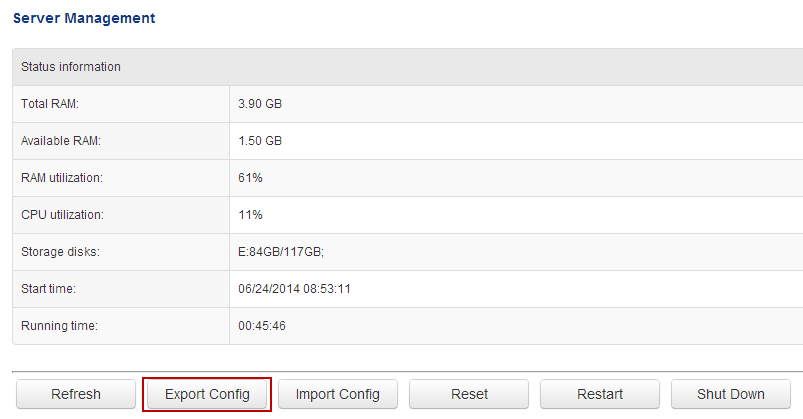
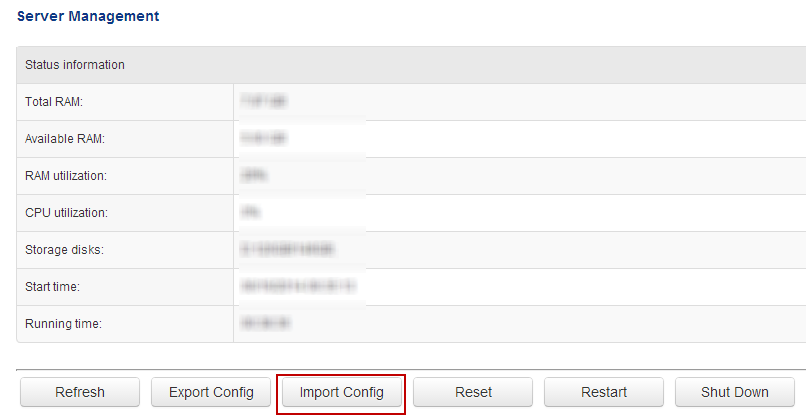
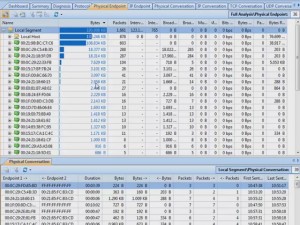
Find out Port Number
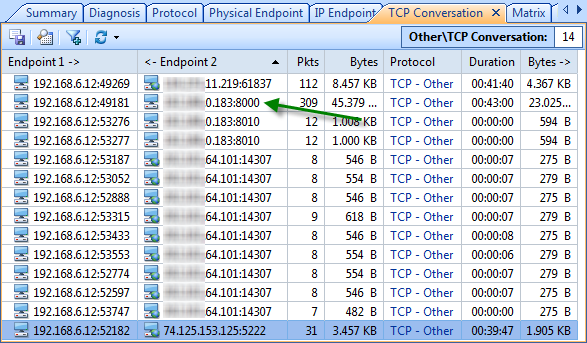
For example, I spot in Capsa Free the following TCP connection suspicious, which constantly communicates to IP: xx.xx.0.183, on port 8000. So I’m going to look up the process name using this port.
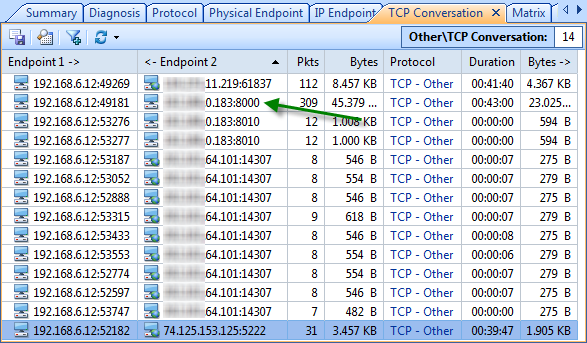
Find Process ID (PID)
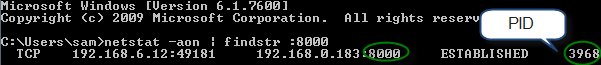
At once I evoke Command Prompt, and entered the following string and hit enter.
netstat –aon | findstr :8000
Explanation:
-a: list all active connections and their ports. –o: show process IDs. –n: display the port numbers numerically.
| findstr :8000: display only the items with string :8000 (findstr means find string). Don’t forget the pipe symbol | at the beginning.
Let’s see what we get.
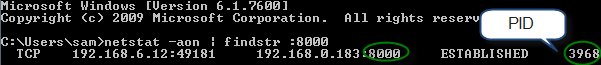
We can read in this case 3968 is the PID, and the source IP address and the target address is the same as the first figure.
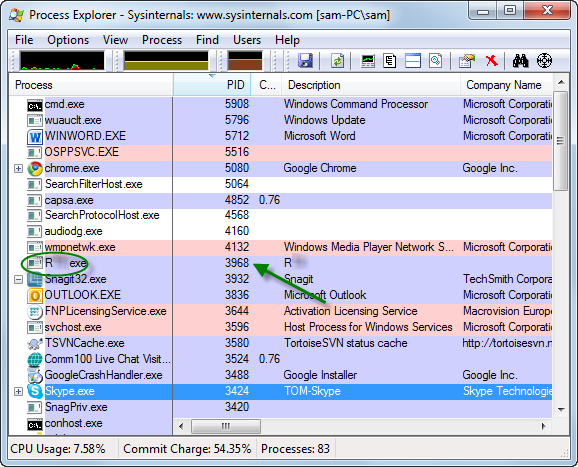
Find Process/Application
Next we’ll switch to another tool Process Explorer (a free tool that you can get from: http://technet.microsoft.com/en-us/sysinternals/bb896653) immediately. And we can easily find out the process or application of this PID: 3968.
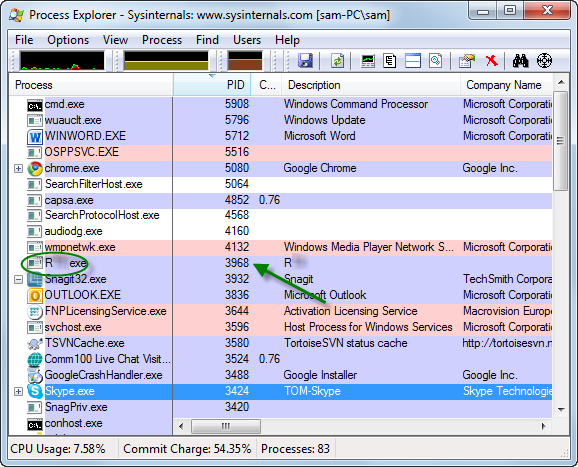
I’m sure it’s an instant messenger used internal in my office and it’s safe. You can also try to find this PID in Windows Task Manager if you don’t have Process Explorer installed.
However task Manager will not provide as much information as Process Explorer. And command prompt is quite handy for geeks.
tasklist | findstr 3968
This command will list only the task items with string 3968. Please refer to previous command if you not sure about | findstr parameter.
Kill Process/Application
So next, you may want to kill a process when you find it’s malicious and want to end it at once? If you are with Process Explorer, you just right-click on a process item and choose Kill Process (Press Del button for short) to kill that process (you can do the same in Task Manager). Again, you may run the following in Command Prompt:
taskkill /F /PID 3968
Explanation:
/F means force to kill the process. And I suppose you understand PID so far.
Now we successfully detect and target the suspicious process with the specific port number, no matter UDP or TCP. And of course this procedure is reversible, you can find out the port number from the process’s PID.